Your Phone May Soon Replace Many of Your Passwords
Credit to Author: BrianKrebs| Date: Sat, 07 May 2022 13:31:17 +0000
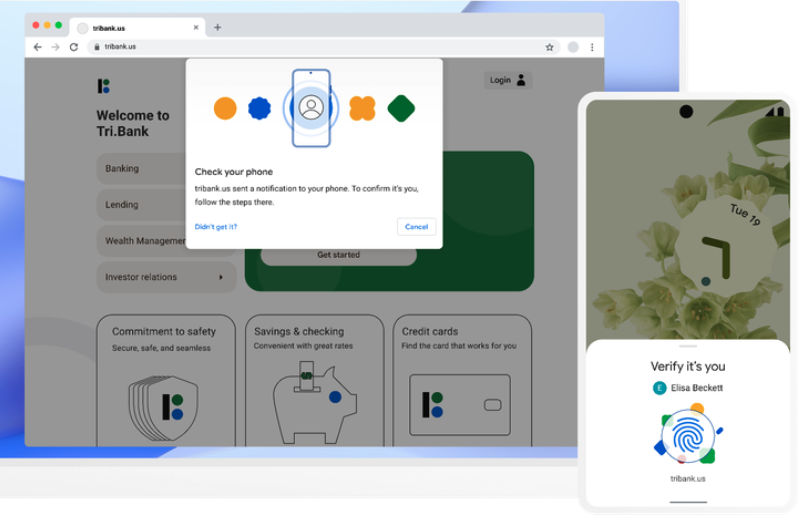
Apple, Google and Microsoft announced this week they will soon support an approach to authentication that avoids passwords altogether, and instead requires users to merely unlock their smartphones to sign in to websites or online services. Experts say the changes should help defeat many types of phishing attacks and ease the overall password burden on Internet users, but caution that a true passwordless future may still be years away for most websites.
Read more