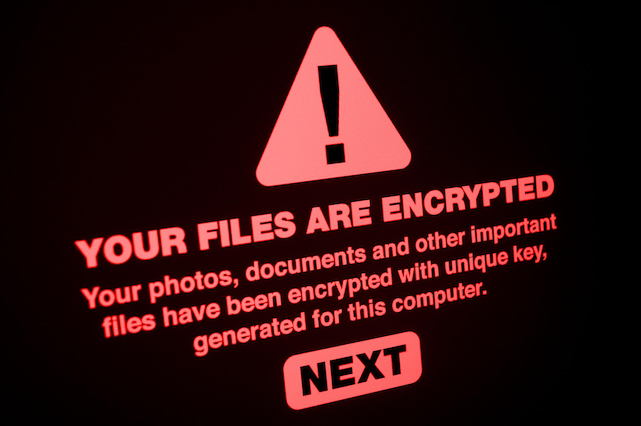
Black Basta Ransomware Operators Expand Their Attack Arsenal With QakBot Trojan and PrintNightmare Exploit

Credit to Author: Kenneth Adrian Apostol| Date: Thu, 30 Jun 2022 00:00:00 +0000
We look into a recent attack orchestrated by the Black Basta ransomware ransomware group that used the banking trojan QakBot as a means of entry and movement and took advantage of the PrintNightmare vulnerability to perform privileged file operations.
Read more