Twitter’s Clumsy Pivot to X.com Is a Gift to Phishers
Credit to Author: BrianKrebs| Date: Wed, 10 Apr 2024 14:28:17 +0000
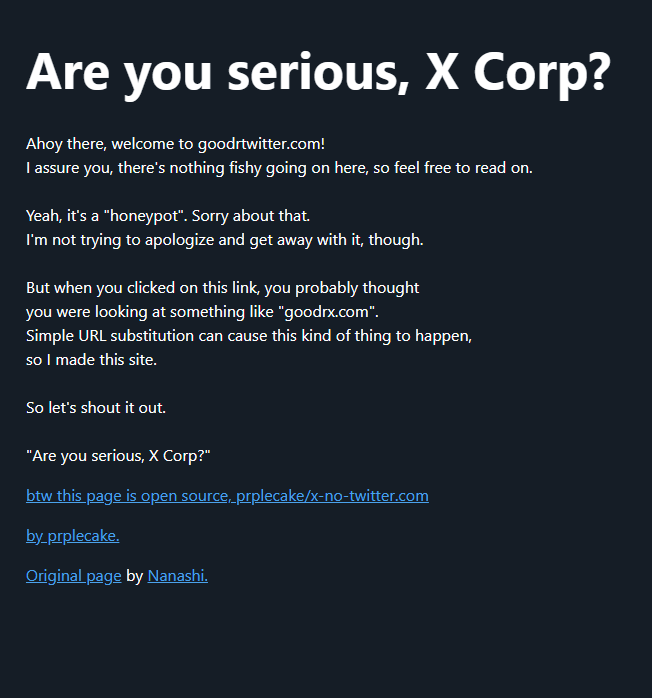
On April 9, Twitter/X began automatically modifying links that mention “twitter.com” to redirect to “x.com” instead. But over the past 48 hours, dozens of new domain names have been registered that demonstrate how this change could be used to craft convincing phishing links — such as fedetwitter[.]com, which is currently rendered as fedex.com in tweets.
Read more